Don't you wanna cry?
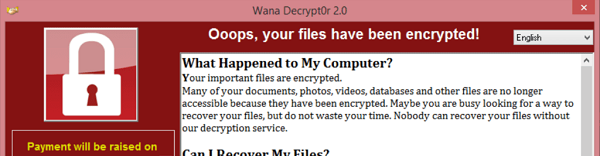
It looks like we're in the middle of one of the worse attacks in the last decade. The WannaCry attack has already crippled more than 230.000 computers, in more than 100 countries.
We already saw big organizations like Telefonica and the NHS, like Renault and Deutsche Bahn having their operations impacted. And it's not over yet. But...
I am so surprised, at this time, to see antivirus and antimalware vendors taking the opportunity to blatantly and shamefully say "if you used our product". The same with Windows 10 advocates, and (I don't believe I write this) Linux advocates. And the same with people blaming the IT departments for not patching in time or not protecting.
This shows a huge misconception about the problem: It's not a technical problem and it cannot be solved by technology. It's clearly a decision / process / support problem.
What is decision / process / support ?
A decision has to be made, by the decision makers of course, that information and IT security are important elements of the service delivery. This goes to the board. This goes to the CIO and the empowerment of the CISO. It's not something the CISO can do on his own. First of all, he does not have the authority without proper decision from above, but additionally, he does not have the resources and access required .
The job of the CISO starts after the decision is made, and his job is to define the process. The architecture, the diligence, to define what needs to be done, what controls need to be in place, what support mechanisms and what processes, how to measure them and how to manage the risk. It's not an easy job, but once the decision is in place, this complicated and crucial job has to be done.
Finally it's the support. I don't know a single company where support is not provided by the IT department. Either internal or external / outsourced. Patches and updates, have to be performed by IT. Problem? Usually IT is understaffed. Indeed, but the IT departments cannot say that security is not their job or they don't do it because they are understaffed. As these are the people with privileged access to the systems and networks, so they are responsible to ensure the systems and networks are up and running securely.
Is it IT to blame?
I would not say so, in general.I know, and have seen it again and again, that IT is a blocker for security. Indeed, the controls that enhance security sometimes make IT unhappy. In how many companies, IT people have more privileges than they need? Probably in most. In how many companies, IT people think that the rules and restrictions don't apply to them? Probably in most. But this does not mean that IT is to blame! As we control other departments, we should control IT too. As we have controls in place that do not allow an HR employee to change his salary as he wishes, we should have controls in place to not allow IT people to bypass security controls as they wish.
The fact remains, that IT in general does not do what should be done for security.
But if you think that Security is the only function that gets crippled by IT's lack of resources, you're wrong.
Another example?
In most companies there is a fight between keeping the lights on, or business as usual, and project needs. Usually the same resources are responsible for both. Yes, the lights are kept on, most of the time.
But at what expense? More than half of IT projects fail. And they fail either due to bad planning (the project manager's responsibility), or due to lack of resources required to execute the project.
Does this ring any bells?
Let me rephrase. More than half of the companies' systems are insecure. And they are insecure either due to lack of design of processes and controls (the CISO's responsibility) or due to lack of resources required to implement the controls.
So clearly, it's not that IT can but does not want to. It is that IT, just cannot if not adequately staffed. Wherever you see a failure, you most probably see a lack of resources problem. Yes, you may also see a failure at the CISO level, or a failure by individual IT people, but these are not the most common. The most common cases, are caused by lack of readiness, lack of hygiene, lack of housekeeping. And these require resources.
These failures cost money. Either you see it as failed projects, or you see it as security incidents, in the end of the day it is money.
So, what do we do?
I would say that the first thing we, as security professionals, do is design and plan. The more we design, the more chances we have to implement properly. Then we automate. The more we automate, the less resources we need.
Then we try to get the decision. The decision I was talking about, to be taken by the board? This one. The one that says that security is important.
Get this opportunity from the WannaCry attack. Calculate the impact it had on your organization. Even if you weren't infected, calculate how many manhours you had to spend for emergency patching and emergency activities. Convert that to money and take it to the board.
Then realize that sometimes, the decision is not there. Some other times, the process is not appropriate. And finally, some other times, the support people don't want to help. But until you have ruled out the first two, stop blaming technologies and the IT people.